Wasabi Protocol Loses $5M After Admin-Key Compromise
An admin-key compromise drained more than $5 million from Wasabi Protocol perpetuals vaults and LongPool across Ethereum, Base, Berachain and Blast.
Wasabi Protocol suffered an admin-key compromise on April 30, 2026, that drained more than $5 million from its perpetuals vaults and LongPool across Ethereum, Base, Berachain and Blast, on-chain security firms Blockaid and PeckShield reported.
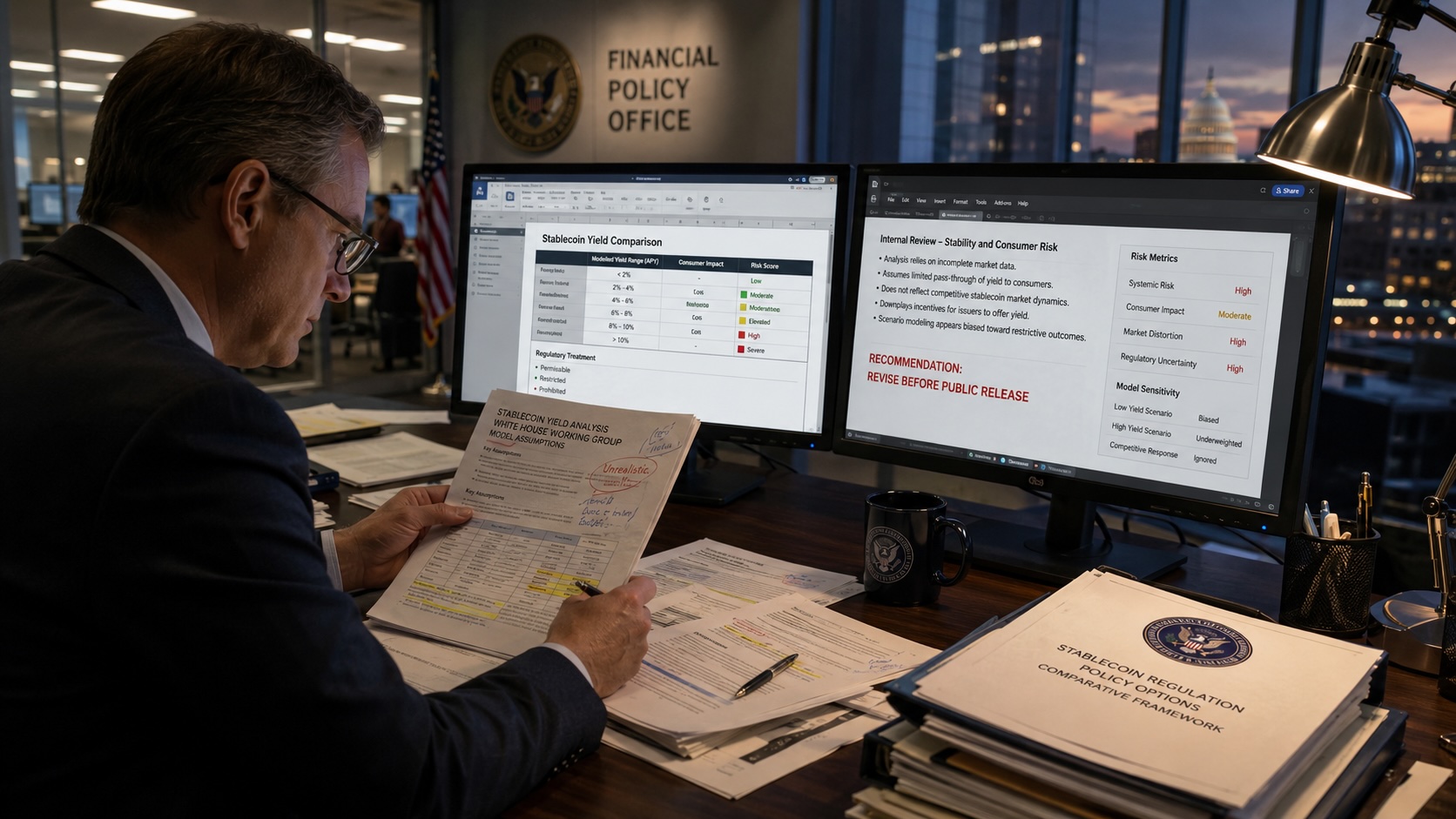
Blockaid’s analysis shows the attacker obtained ADMIN_ROLE by calling grantRole on the protocol’s deployer externally owned account with zero delay, immediately elevating an orchestrator contract to admin. The attacker then used the UUPS upgrade mechanism to replace vault implementations with malicious code and siphon funds. Blockaid counted about $4.55 million extracted at the time of its report; PeckShield put total losses across the four chains above $5 million. The deployer key used to carry out the changes remains active.
Wasabi Protocol warned users not to interact with its contracts while teams investigate. “We’re aware of an issue and are actively investigating. As a precaution, please do not interact with Wasabi contracts until further notice,” the protocol posted. Tokens tied to affected vaults, including Spicy LP-share tokens, have been flagged as compromised and their redemption value is approaching zero.
Blockaid linked the bytecode of the attacker’s orchestrator and strategy contracts to earlier activity that targeted Wasabi, indicating the same actor or toolkit may be involved. The security firm noted the root cause traced to wasabideployer.eth, the only address holding ADMIN_ROLE in Wasabi’s PerpManager AccessManager, and the absence of timelocks or multisignature controls on that account.
The Wasabi incident occurred hours after several other DeFi losses: a $3.46 million drain at Sweat Economy later described as a foundation rescue; a bridge incident on Base that moved 18.5 million SYND tokens (roughly $330,000 to $400,000) to Ethereum; and a pause at a perpetuals protocol following a roughly $1.14 million USDC loss.
Some developers and analysts have raised the possibility that advanced automation, including AI-assisted exploit tooling, may be influencing the pace of recent attacks. Developer Vitto Rivabella wrote on social media that a trained model could run autonomous exploit campaigns, describing the idea as a “wild conspiracy theory” about state-backed AI tools.
ADMIN_ROLE grants an address the ability to perform high-level management actions, including contract upgrades. The vaults used an upgradeable proxy pattern that allows an admin to swap implementation code. When a single private key controls that admin account and no timelock or multisig is enforced, anyone who gains access to the key can immediately change code to add withdrawal routines and extract funds.
Investigations into the Wasabi drain are ongoing. Security firms and Wasabi teams continue to analyze on-chain evidence and monitor related activity.